How Safe Are Your Smart Home Devices?: A Simple Guide for IoT Security and Awareness
By Saqib Sharif ||
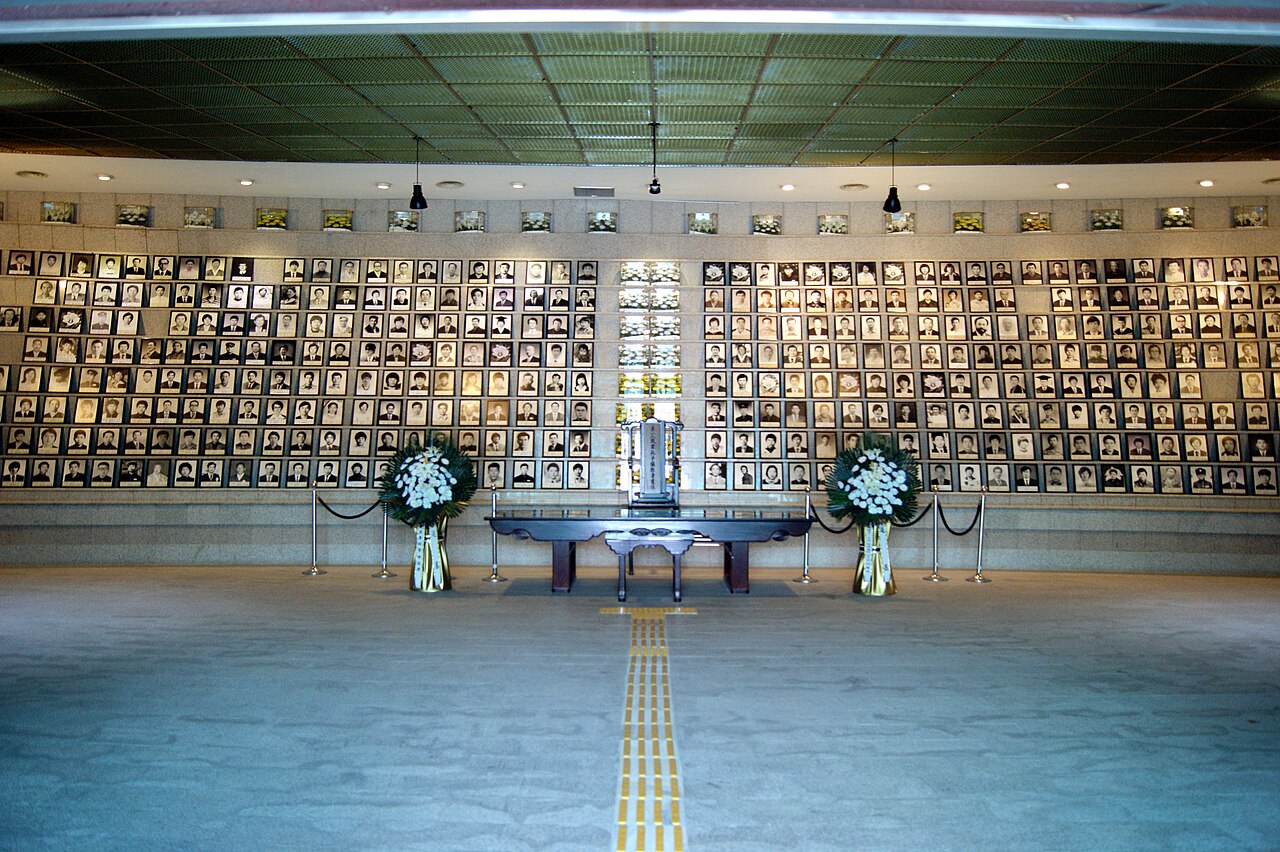
Over 120,000 home cameras in South Korea were hacked, with attackers gaining access to private footage and using it for illegal purposes, including distributing intimate recordings. This BBC story serves as a stark warning about how easily everyday internet-connected devices can be compromised when they are not properly secured, and how deeply such breaches can affect people’s privacy and safety.
Smart home gadgets, cameras, sensors, locks, light bulbs, and more are all part of the so-called Internet of Things (IoT). These devices are meant to make life more convenient by connecting to the internet or to each other so you can control them with an app or voice commands. But while convenience is great, it comes with a trade-off: Every device you connect to your network is a potential door into your home for cybercriminals.
Research by security experts shows that attacks against IoT devices are rising rapidly, with millions of attempts to exploit weak devices around the world every day. Many smart devices do not use Wi-Fi alone to talk to each other. Instead, a popular way for them to communicate is through ZigBee, a wireless system designed specifically for small, low-power devices that need to send simple messages like “turn on,” “light is on,” or “motion detected.” ZigBee is popular because it uses very little power; tiny sensors can run for long periods without frequent battery changes. It also supports something called a mesh network, which quietly connects many devices together so that signals can hop from one to another until they reach their destination.
A ZigBee network works almost like a team passing messages along. One device in your home, usually the main smart hub, acts as the coordinator. It is the central point that manages the ZigBee system and links it to your wider home network and the internet. Around it are devices that act as routers; these are typically things that are always powered, like smart plugs or wall switches. They help forward messages across the network so devices that are far away from the hub can still communicate. Then there are the smaller end devices, such as sensors and buttons. These send and receive messages but do not pass them on to others. Together, all these connections form the ZigBee network map, where each device is like a dot linked to others: Messages take the best available path to reach the hub and then the internet. This makes the system flexible and reliable, even in large homes.
One of the best things about ZigBee is that it uses encryption, a kind of secret code, to protect communication between devices much like banks use encryption to protect financial data. But this protection can only work well if all the devices in the network are secure. If one device has weak security, outdated software, or a default password that’s easy to guess, it breaks the chain of trust. A hacker might be able to join the ZigBee mesh through that weak device and start listening to traffic or even sending their own commands.
“Private footage can be stolen, personal routines exposed, and sensitive information misused.”
This is especially risky when you add third-party devices; that is, gadgets made by a different company than your main smart hub brand. These products are often cheaper or promise extra features, but they may not have strong security practices. Because ZigBee devices automatically trust others once they join the network, a poorly secured third-party device is like a poorly locked window in your house. An attacker might not immediately take over everything, but they can use that access point to watch activity, intercept communication, or look for other weaknesses in your network that let them go further.
Once a device becomes part of the network, even if it only exchanges small, encrypted messages, it can still leak useful information. Security researchers have shown that attackers do not always need to read the actual data. By simply watching when devices communicate, how often they send messages, and which devices respond, it is sometimes possible to guess what is happening inside a home. Over time, this can expose daily routines and behavior patterns without ever breaking the encryption itself. Because of this risk, it is always recommended to avoid ultra-cheap online IoT devices that seem too inexpensive for the features and services they promise, as such products often cut corners on security to reduce costs.
The South Korean camera hack shows how serious these risks can be in real life. When cameras or other home devices are compromised, the impact goes beyond annoying pop-up ads or glitches. Private footage can be stolen, personal routines exposed, and sensitive information misused. This isn’t just theoretical; real people have had their privacy violated and suffered emotional and personal consequences as a result.
Understanding how ZigBee and other IoT networks work helps explain why these systems need better security. Each device you add increases the size of your network and the number of potential weak points. Convenience shouldn’t mean that privacy and safety are ignored. Choosing reputable devices, keeping them updated, changing default passwords, and thinking carefully before adding random products to your smart home can make a meaningful difference in protecting your digital life.
Sources
- Butler, G. (2025, December 1). More than 120,000 home cameras in South Korea hacked to record “sexploitation” footage. BBC News. https://www.bbc.com/news/ articles/cj01q6p7ndlo
- Seals, T. (2015, August 7). #BlackHat: Critical ZigBee flaw compromises smart home devices. Infosecurity Magazine. https://www.infosecurity-magazine.com/ news/blackhatcritical-zigbee-flaw-smart/
- Connectivity Standards Alliance. (n.d.). The full-stack solution for all smart devices. https://csa-iot.org/all-solutions/zigbee/
The Author
Saqib Sharif is a robotics engineer with a PhD in mechanical engineering, specializing in the design of smart healthcare devices and microrobots. With a strong background in medical technology and innovation, he is passionate about creating solutions that enhance smart healthcare. Dr. Sharif has been living in Gwangju for the past ten years. Currently, he serves as a senior researcher at Shinsung Tech Pvt. Ltd., Gwangju.
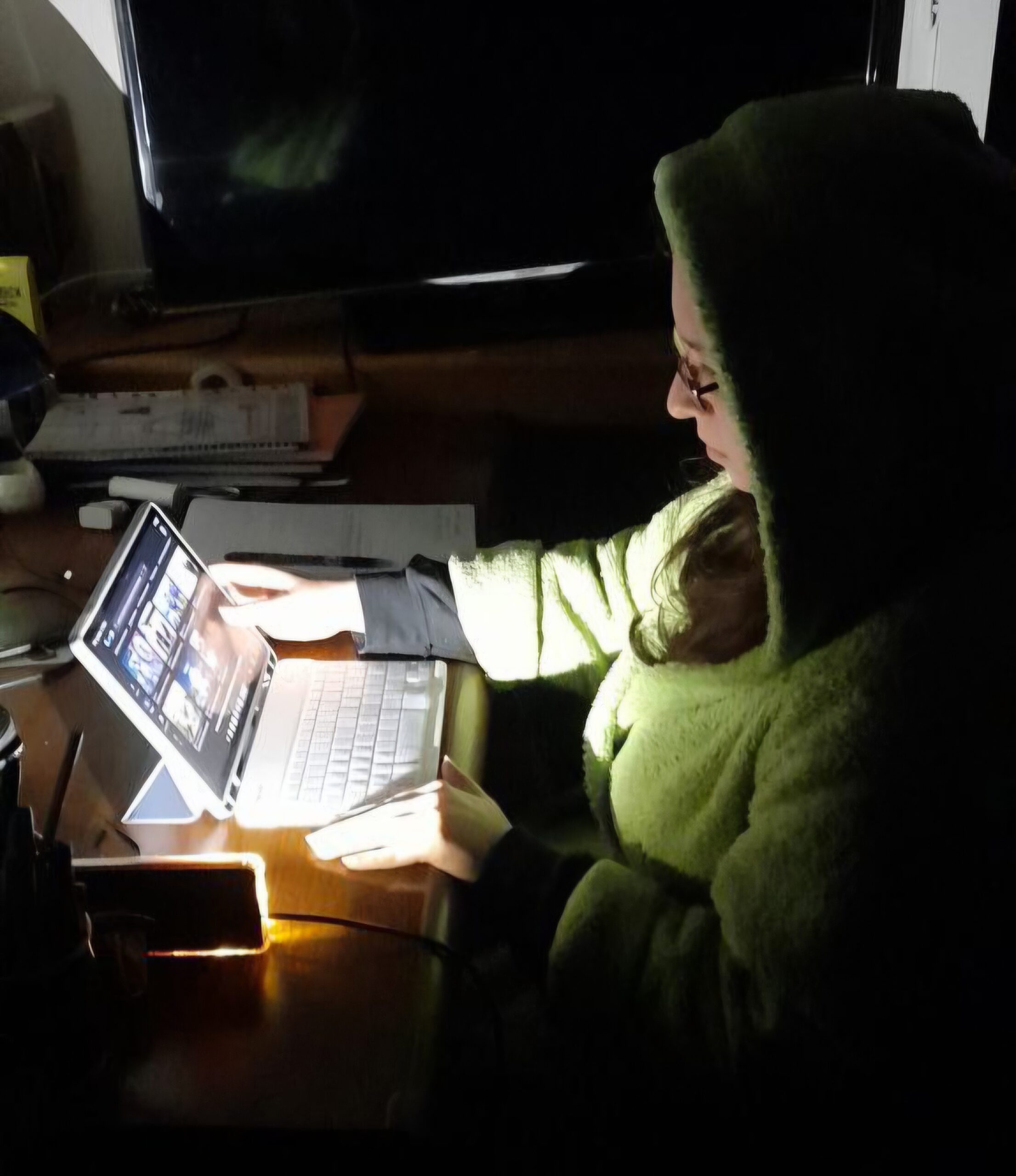
Cover Photo: The smart home nightmare and the IoT exploit.